What are the psychological functions of privacy ? What do the psychologists and “academicians” who have looked into it actually have to say about it ? Can we be inspired by some of their findings to better protect privacy, and/or maybe fix the “argumentative gap” with a public too prompt to resolve the problem with the “I have nothing to hide” argument ?
Researching the socio-psychological functions of privacy through its literature in social sciences I find that the works of Westin, Pedersen, Altman seem to have been influentials, ever since they were published already some years ago. Their “models” and understanding of the complex concept of privacy have inspired researchers after them.
Alan Westin, for instance, author of Privacy and Freedom, identified 4 types of privacy : solitude, intimacy, anonymity and reserve – and 4 functions of privacy : personal autonomy, emotional release, self-evaluation, and protected communication
Darhl M Pedersen, contributed numerous research on the subject in social psychology, starting with The Psychological Functions Of Privacy, where he empirically identified 5 functions of privacy: contemplation, autonomy, rejuvenation, confiding and creativity.
Environmental psychologist Irwin Altman also researched and wrote about personal space and privacy.
I came across a Literature review on the subject of privacy inside another article TOWARDS A PRIVACY FRAMEWORK FOR INFORMATION SYSTEMS DEVELOPMENT, by Peter J. Carew and Larry Stapleton.
Here it is below.
2. PRIVACY: A REVIEW OF THE LITERATURE
The concept of privacy appears in the literature of several disciplines. There is no universal definition for privacy, and numerous authors have highlighted the difficulties in producing such a definition (cf. Burgoon, 1982; Leino-Kilpi, et al., 2001; Newell, 1998). Theorists argue over whether privacy is a condition, a process or a goal (Newell, 1998). While privacy may be a difficult concept to characterise concisely, the various definitions do have substantial commonalities. One group of definitions emphasise seclusion, withdrawal, and avoidance of interaction with others. The second group puts more emphasis on the control individuals have over their lives.
There are a number of formal models of privacy in the literature, but the theories of Alan Westin (e.g. Westin, 1970) and Irwin Altman (e.g. Altman, 1976) are considered authoritative. Their theories and ideas have stood the test of time and have been the basis of research for many subsequent authors (Margulis, 2003; Pedersen, 1999, 1997; Petronio, 1991). The remainder of this section provides an aggregated overview of some of the core aspects of privacy compiled from the most influential literature. These core aspects set out the theoretical background against which any ISD privacy theory must be constructed.
TOWARDS A PRIVACY FRAMEWORK FOR ISD
3 2.1. Privacy Types, Functions and Mechanisms
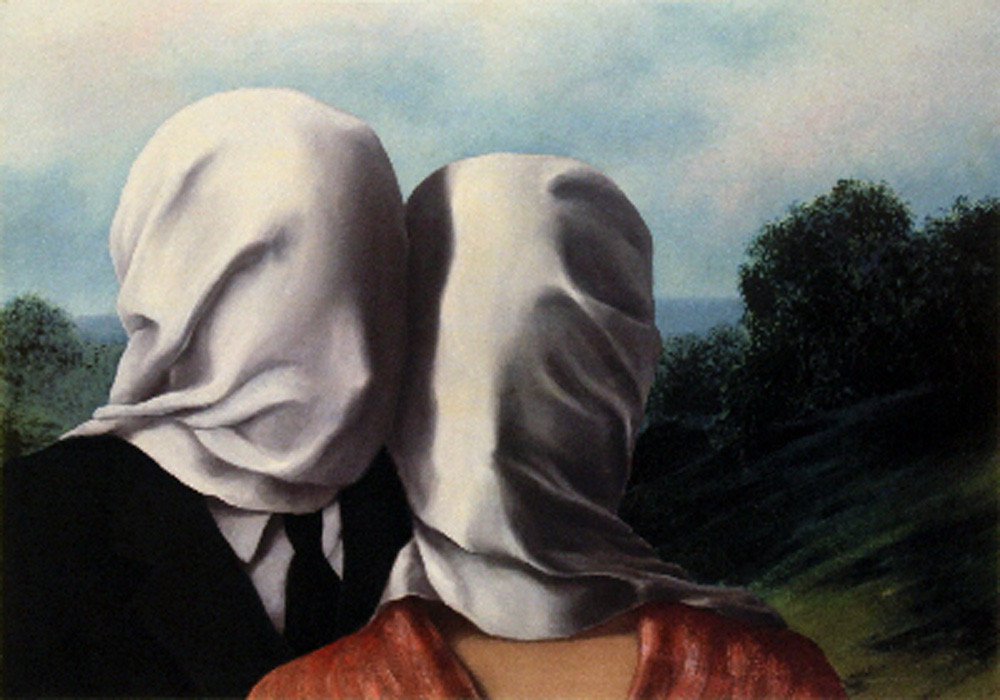
People experience and desire several states, or types, of privacy. These include the four identified by Westin (1970): solitude, intimacy, anonymity and reserve. Solitude means to be alone and free from observation by others. Intimacy refers to being alone with a small group to the exclusion of others (e.g. family), and concerns close relationships. Anonymity refers to being unrecognised in a public place – to be inconspicuous and blend into the crowd. Reserve is based on a desire to limit disclosures to others. Pedersen (1997, 1999) extended Westin‟s model by adding isolation (i.e. using physical distance to be alone) and splitting intimacy into intimacy with family and intimacy with friends. Burgoon (1982) identified the following broad dimensions of privacy: social, physical, informational and psychological.
Privacy functions refer to why individuals seek privacy. Westin (1970) identified four functions of privacy: personal autonomy, emotional release, self-evaluation, and limited and protected communication. Personal autonomy relates to independence and self-identity. It is the desire to avoid being manipulated, dominated or exposed by others. Emotional release refers to freedom from the tensions of social life, and being able to deviate from social norms, roles, rules and customs safely. Self-evaluation refers to integrating experience into meaningful patterns, and the opportunity to plan and assess future actions (i.e. self-reflection and assessment). Limited and protected communication provides the opportunity to share personal information with trusted others. Altman (1976) describes three functions of privacy: interpersonal, the interface to the self and the social world, and self-identity. Pedersen (1997, 1999) empirically identified five basic functions of privacy: contemplation, autonomy, rejuvenation, confiding and creativity. From a systems point of view, Newell (1998) argues that privacy provides an opportunity for restabilisation, system maintenance (i.e. healthy physiological and cognitive functioning) and system development (i.e. towards autonomy and self-actualisation). Individuals may seek to protect their privacy to avoid e.g. embarrassment, harassment, ridicule, shame, scrutiny or discrimination (Shapiro and Baker, 2001).
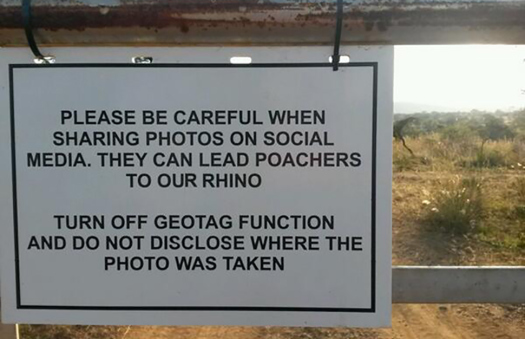
Behavioural mechanisms are used to achieve a desired level of privacy. These mechanisms include verbal, paraverbal (e.g. tone), non-verbal (e.g. gestures), environmental behaviour (e.g. personal space and territoriality), and cultural norms and customs (Altman, 1976; Pedersen, 1999). Personal space is an invisible zone surrounding the human body, separating people from one another (Leino-Kilpi, et al., 2001). Territoriality refers to a perceived ownership of areas, objects, knowledge or status. These privacy mechanisms function as an integrated system, supporting and substituting each other as appropriate (Altman, 1976).
2.2. Circumstance, Individuality and Culture
Privacy interests vary in both content and magnitude across situations and individuals. What may be trivial to one individual may be significant to another (Shapiro and Baker, 2001). Relevant personal factors include the individual‟s need for privacy, personal attractiveness, interpersonal skills, personality variables, and ability to use privacy control mechanisms effectively (Pedersen, 1999). Personality variables include extraversion, emotional stability, agreeableness, openness to experience, and conscientiousness (Zweig and Webster, 2003). Gender also can impact on privacy preferences (Newell, 1998; Pedersen, 1999). Some cultures have a stronger preference for privacy and more privacy needs than others (Kaya and Weber, 2003). The need for privacy is universal but manifestations and privacy mechanisms are culturally specific (Margulis, 2003; Newell, 1998). For example, local culture has been shown to affect people‟s perceptions of crowding (Hall, 1966).
2.3. Intrusion and Privacy Violation
Intrusion essentially is when the desired level for privacy is higher than the actual level being enjoyed (Altman, 1976). Altman‟s process oriented model for social interaction is useful for further describing what is meant by intrusion or privacy violation. In Altman‟s theory, privacy has five properties: units of privacy, the dialectic nature of privacy, the non-monotonic nature of privacy, privacy as a boundary control process, and privacy as a bi-directional process (Altman, 1976). Units of privacy refer to the fact that privacy applies at the individual and group levels, and differences exist in privacy dynamics for various social units (Altman, 1976; Margulis, 2003). The units of privacy can be person-to-person, person-to-group, group-to-person or group-to-group (Leino- Kilpi, et al., 2001). The dialectic nature of privacy refers to the fact that individuals continuously change their desire for interpersonal contact. There are two opposing forces at work at all times – one drawing individuals together, and another pushing them apart. Privacy can, thus, be viewed as a dynamic, dialectic process where the need for solitude and the need for interpersonal contact are constantly in opposition. The desired level of privacy depends on which of the two opposing forces is strongest at a given time. The non-monotonic nature of privacy refers to the fact that there is an optimal level of privacy at a given time, and people can have too much privacy (e.g. social isolation) or too little privacy (e.g. crowding). Privacy as a boundary regulation process offers the notion of a flexible barrier between the self and non-self, which can be opened or closed depending on circumstance (Altman, 1976; Petronio, 1991). Finally, privacy can be viewed as a bi- directional process, involving controlling inputs from others and outputs to others.
In terms of Altman‟s model, intrusion therefore depends on a number of factors. Different social units have different privacy needs (e.g. family, work group, individual), these needs change frequently, and it is possible to have too much or too little privacy. While too much interaction may be experienced as an invasion of privacy, too little may be experienced as loneliness or alienation (Pedersen, 1999). Being forced to interact (i.e. receive input or provide output) beyond the level of interaction desired in a given circumstance is an intrusion as the forced participation implies an attempt to break through the flexible mental barrier (cf. Altman, 1976). The ability to control interactions is essential for privacy management.
Technology has long been recognised as posing a significant threat to the privacy of personal data. The following section looks at some of the privacy related ethical issues in the information society. It shows how ICT is shaping society and the workplace and highlights some dilemmas facing the ethical ISD professional.
P. Carew, and L. Stapleton (2005). „Towards a Privacy Framework for Information Systems Development‟, in O. Vaselicas, W. Wojtowski & G. Wojtowski (eds.), Information Systems Development: Advances in Theory, Practice and Education, Kluwer Academic Press/ Plenum