Dans une analyse du 17 mars 2021, La Quadrature du Net expose les soubassements idéologiques du projet français de centralisation des données de santé, le Health Data Hub, entouré des fantasmes d’I.A et de compétitivité. Elle alerte sur ses dangers, depuis les atteintes à la vie privée jusqu’à l’accélération vers un système de santé déshumanisé, et demande :
- L’arrêt du développement du HDH, dans l’attente d’une remise à plat de ses objectifs et son fonctionnement ;
- L’arrêt du contrat d’hébergement conclu avec Microsoft
- Un changement de paradigme faisant de l’accès aux données de santé de la population française par le secteur privé l’exception plutôt que la norme.
“Projet central du « Plan national pour l’intelligence artificielle » (surnommé « AI for humanity« ), le « Health Data Hub » (HDH) est un projet visant à centraliser l’ensemble des données de santé de la population française. Il est prévu que le HDH regroupe, entre autres, les données de la médecine de ville, des pharmacies, du système hospitalier, des laboratoires de biologie médicale, du dossier médical partagé, de la médecine du travail, des EHPAD ou encore les données des programmes de séquençage de l’ADN [1].
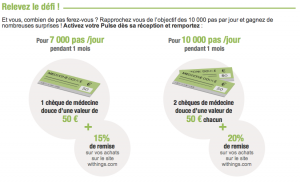
Le HDH se substitue à une structure existante, le Système National de Données de Santé, avec deux principales modifications : un large élargissement des données collectées et un accès facilité, en particulier pour le secteur privé (GAFAM, « medtechs », startup, assureurs…), à ces dernières. A noter que les décrets officialisant les critères de sélection des projets ayant accès aux données ne sont toujours pas parus. Son objectif est donc, via leur centralisation, de faciliter l’utilisation de nos données de santé par le plus grand nombre d’acteurs de manière à, selon ses promoteurs-rices, « faire de la France un pays leader de l’intelligence artificielle » [2].
Ce projet, mené sans réelle concertation publique, est au centre de nombreuses controverses. Le choix du gouvernement de confier son hébergement à Microsoft, dans l’opacité la plus totale et malgré un avis particulièrement sévère de la CNIL, a soulevé de nombreuses protestations. Alors même que les critiques s’intensifiaient, le gouvernement a profité de l’état d’urgence sanitaire pour accélérer son développement, décision qui fut attaquée en justice par le collectif Interhop. Edward Snowden lui-même a pris position contre ce projet en dénonçant une capitulation du gouvernement devant « le cartel du Cloud ».